| 技術名稱 | 利用韌體檢測與硬體模擬的商用物聯網設備安全檢測平台 | ||
|---|---|---|---|
| 計畫單位 | 國立臺灣科技大學資通安全研究與教學中心 | ||
| 計畫主持人 | 鄭欣明 | ||
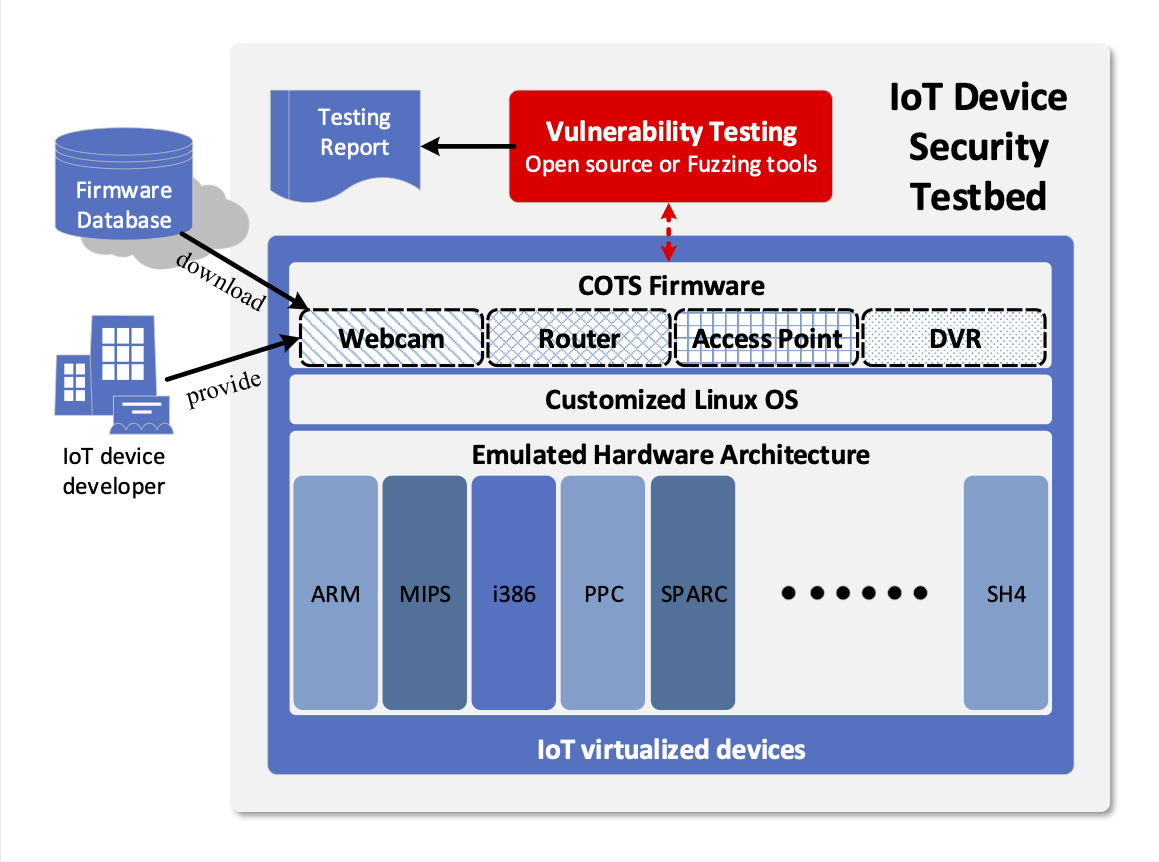
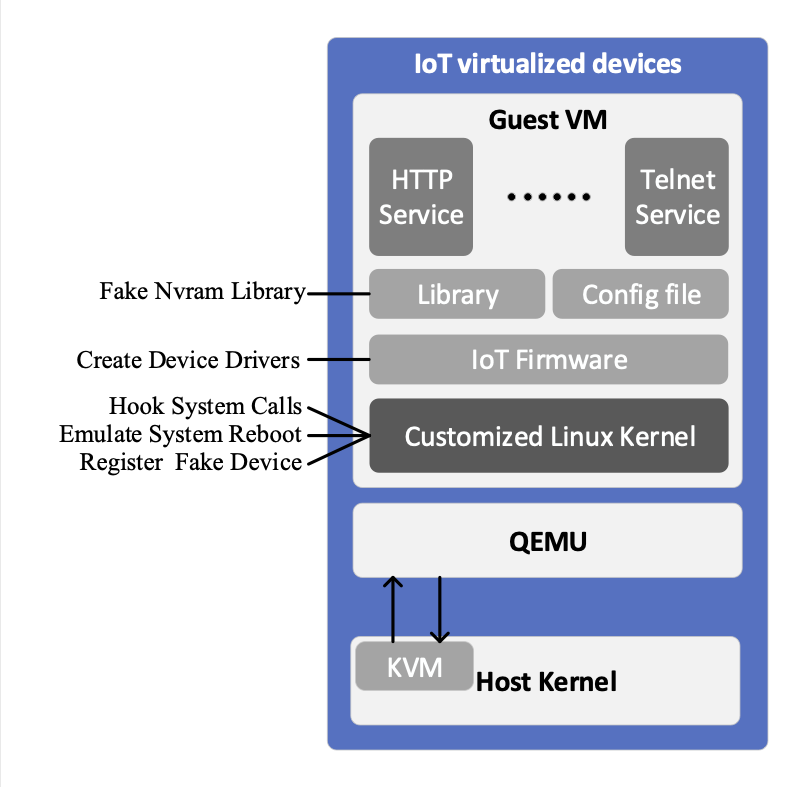
| 技術簡介 | 傳統在檢測成千上萬的且具有不同硬體架構物聯網設備的資安能力時,檢測者必須連接實體物聯網設備,所以擴展性差、容易受到環境限制且效率不彰。本發明即希望開發一個自動化的物聯網設備安全檢測平台,透過虛擬(virtualized)且模擬化(emulated)受檢的商用物聯網設備,可以大幅提升檢測的效率與擴展性。然而,為了讓模擬的商用物聯網設備與實體設備的運作行為完全一致,我們必須完整模擬設備的硬體架構、作業系統並讓設備的韌體能在上面實體運作,其成為本發明的核心關鍵技術。 |
||
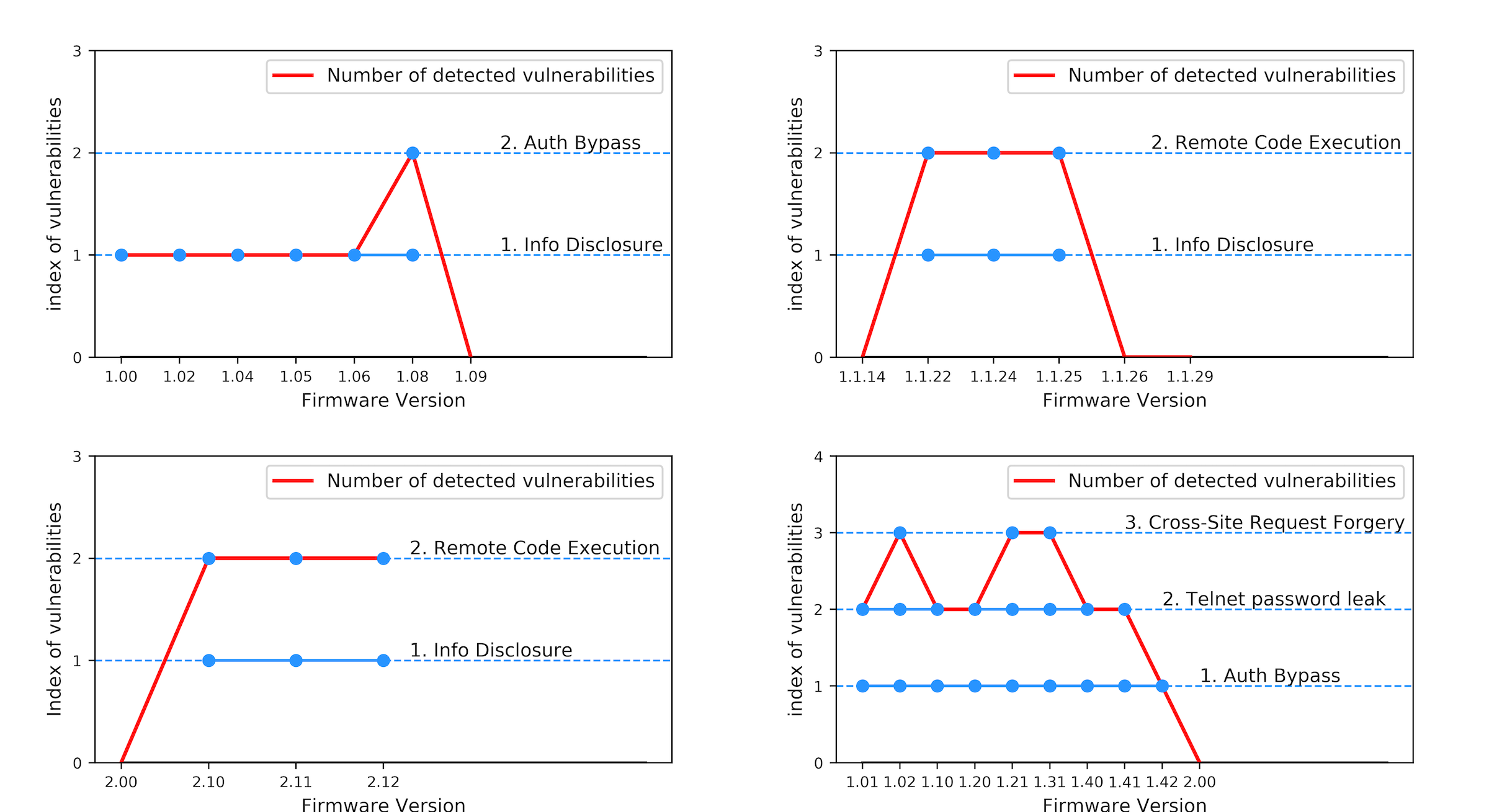
| 科學突破性 | 本檢測平台成功地將多種商用物聯網設備(如Dlink、Zyxel、Netgear等)的韌體安裝在多種模擬的物聯網硬體架構(如AMR、X86、MIPS)上然後加以檢測,如此動態分析的方式比目前靜態分析原始碼方式更能真實捕捉未知或零時差的威脅;也比直接介接實體設備除錯埠來檢測的方式更方便且有效率。 |
||
| 產業應用性 | 本檢測平台可獨立或整合於與商用物聯網設備的開發企業,在產品上市前透過檢測商用物聯網韌體,有效率且大規模地挖掘可能的資安漏洞與弱點,並反饋給委託或者合作的企業,讓其在物聯網設備上市之前修正潛在的威脅與漏洞,成為商用產品開發週期中的重要元素。如此可大幅降低上市之後發現漏洞召回設備修補的花費或相關的責罰。 |
||
| 關鍵字 | 商用物聯網設備 設備虛擬化 動態分析 韌體檢測 模糊測試 硬體模擬 物聯網惡意程式 物聯網安全 安全檢測平台 漏洞檢測 | ||
- 聯絡人
- 鄭欣明
- 電子信箱
- smcheng@mail.ntust.edu.tw
其他人也看了