| 技術名稱 | 機敏資料分析的雲端計算信據平台 - 以醫療資料為例 | ||
|---|---|---|---|
| 計畫單位 | 國家實驗研究院國家高速網路與計算中心 | ||
| 計畫主持人 | 林錫慶 | ||
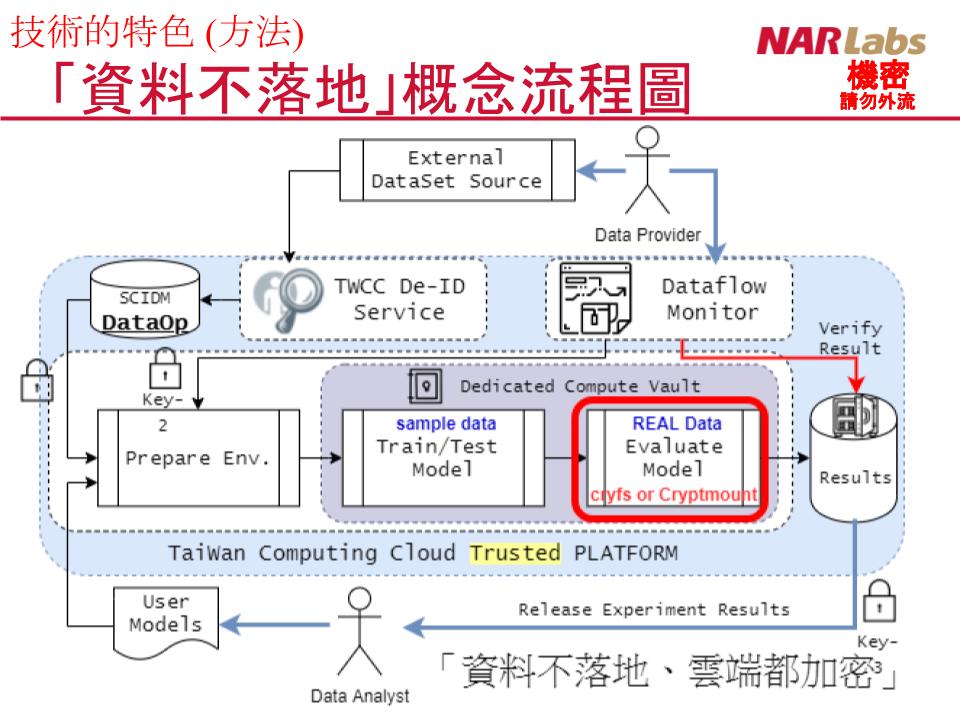
| 技術簡介 | 本項技術基於 TWCC 臺灣 AI 雲平台裡的臺灣杉二號進行技術服務佈署及設計,主要的目標為「希望資料擁有者及資料分析師都能信任的加密計算平台,提供兩者間機敏資料可被取用機會」。 |
||
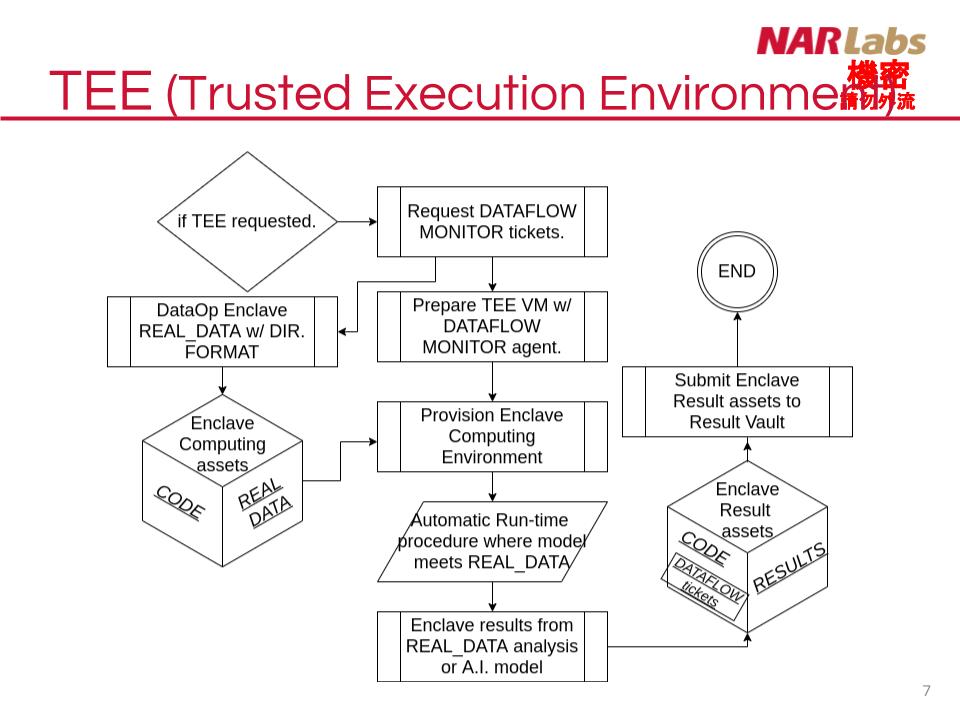
| 科學突破性 | 透過 TWCC 國建國造的雲計算平台,提供機密資料分析需要的信任計算環境,並確保各項分析資料分析的結果,亦需要資料擁有者審視結果是否含有直實資料後,後方可釋出。 |
||
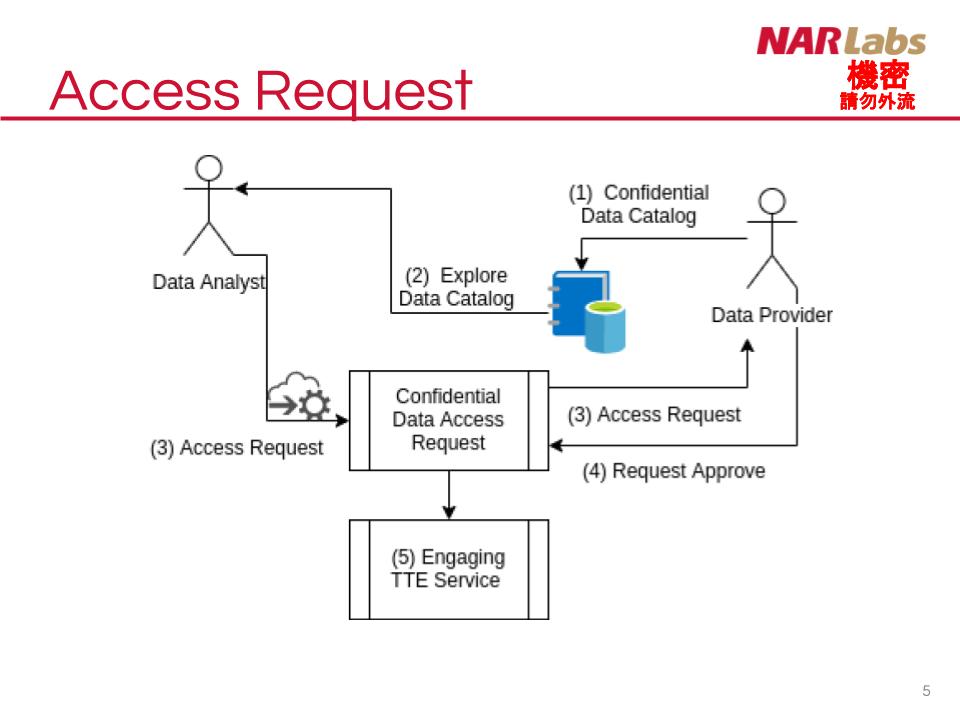
| 產業應用性 | 雲平台業者在面對公私部門使用時,最大的挑戰即為資料安全。在資料提供者方面,完整且具加密的資料流程及資料暫存區機制確保資料完整性。資料取用過程除需經資料提供者同意資料取用,亦需第三方身份認證確保資料不被授與的資料分析者使用,過程全程加密亦不會被雲平台維運人員取得,此流程同時俱備資料保密性。 |
||
| 關鍵字 | 雲端計算 信任計算 機敏資料分析 | ||
| 備註 | 謝謝! |
||
- 聯絡人
- 趙逢毅
- 電子信箱
- 1803001@narlabs.org.tw
其他人也看了